The following topics will be discussed in this post.
- Firewall Protection
- Antivirus Software
- Data Encryption
- Multi-Factor Authentication
- Virtual Private Network (VPN)
In today's digital age, cybersecurity is essential for any business to protect its data and information from malicious actors. Cyberattacks can cause significant damage, including financial loss, loss of reputation, and legal implications, which is why it's crucial to invest in IT solutions to secure your business's sensitive information.

In this blog post, we'll explore the various IT solutions available to maximize your business's security.
Firewall Protection
A firewall is a network security system that provides a barrier between your internal network and the internet, which helps prevent unauthorized access to your network.
By monitoring and controlling all network traffic based on security rules that are stipulated by your IT manager, a firewall can help safeguard your network against cyber threats like malware, phishing, and hacking.
If you want an expertly configured firewall solution but don’t trust the skills of your internal team to secure yours appropriately, then consult with qualified business IT support professionals who can guarantee that all the latest procedures are followed and adhered to.
Antivirus Software
Antivirus software is designed to detect, prevent, and remove malware from your computer systems by scanning your files and system memory for signs of malicious code and blocking or quarantining any threats it finds.
Antivirus software is critical because it protects your business from a range of threats, including viruses, Trojans, spyware, ransomware, and adware. There are several types of antivirus software available, including free and paid versions.
Free antivirus software is a good starting point, but it may not offer the same level of protection as paid versions, which typically include more advanced features like real-time scanning, automatic updates, and enhanced malware detection.
It's worth investing in a reputable antivirus solution, so you can have peace of mind knowing that your business is protected against the latest threats.
Data Encryption
Data encryption is the process of converting plain text into an illegible format to prevent unauthorized users from being able to read them. Encryption is essential for businesses that deal with sensitive data, including financial information, customer data, and trade secrets.

There are two primary types of encryption, although both use keys to encrypt and decrypt data. The first type, called symmetric encryption, uses a single same key to encrypt and decrypt data.
By comparison, asymmetric encryption uses two keys – a public key and a private key – to achieve the same result. Asymmetric encryption is typically more secure, but it's also more complex to implement.
In addition to protecting your data from hackers and other malicious actors, data encryption can also help your business comply with data privacy regulations like GDPR and CCPA.
Multi-Factor Authentication
Multifactor authentication is an IT solution that requires users to provide two or more forms of identification to access a system. This adds an extra layer of security to your business's systems, making it more challenging for hackers to gain access.

Multifactor authentication typically requires users to provide a password and another form of identification, like a fingerprint or security token.
Virtual Private Network (VPN)
A virtual private network (VPN) is an IT solution that provides secure and private access to the internet. It creates a secure connection between a user's device and a remote server, encrypting all data transmitted between them.
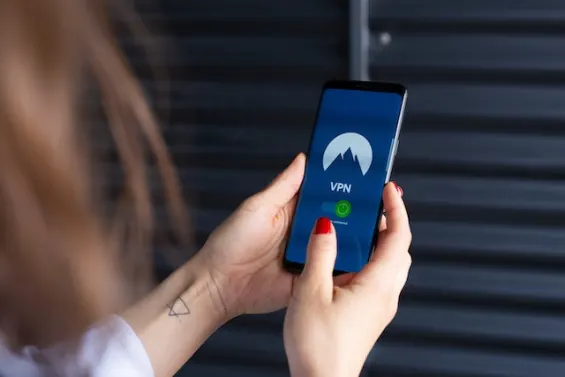
A VPN is particularly useful for businesses that allow their employees to work remotely or from public Wi-Fi networks, as it protects their sensitive information from cyber threats.
Cybersecurity threats are a constant concern for any business operating in today's digital age. It's essential to take proactive measures to protect your business's sensitive data and information.
However, it's also important to remember that cybersecurity is an ongoing process, and it's vital to regularly review and revise your IT security measures to ensure they remain effective.
Read Next
The following articles are related to 5 top it services that help keeping your business secure.